Which type of address is shared by routers in a HSRP implementation and used by hosts on the subnet as their default gateway address?
An engineer must configure a core router with a floating static default route to the backup router at 10.200.0.2.
What is the functionality of the Cisco DNA Center?
Refer to the exhibit.
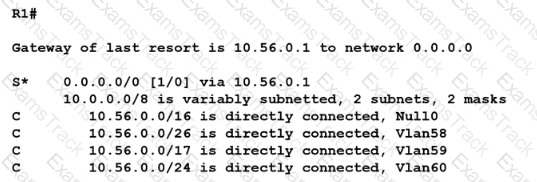
When router R1 receives a packet with destination IP address 10.56.0 62. through which interface does it route the packet?
What is used as a solution for protecting an individual network endpoint from attack?
What is an advantage of using auto mode versus static mode for power allocation when an access point is connected to a PoE switch port?
What is a reason to configure a trunk port that connects to a WLC distribution port?
Refer to the exhibit.
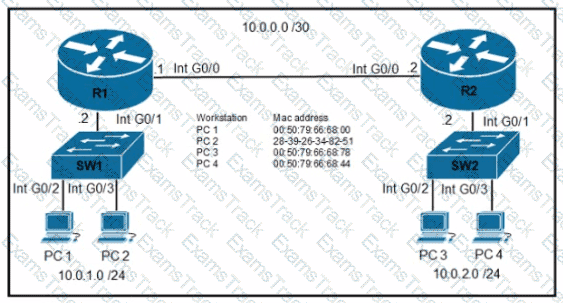
An engineer must configure the interface that connects to PC 1 and secure it in a way that only PC1 is allowed to use the port No VLAN tagging can be used except for a voice VLAN. Which command sequence must be entered to configure the switch?
A)
B)
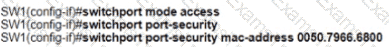
C)
D)

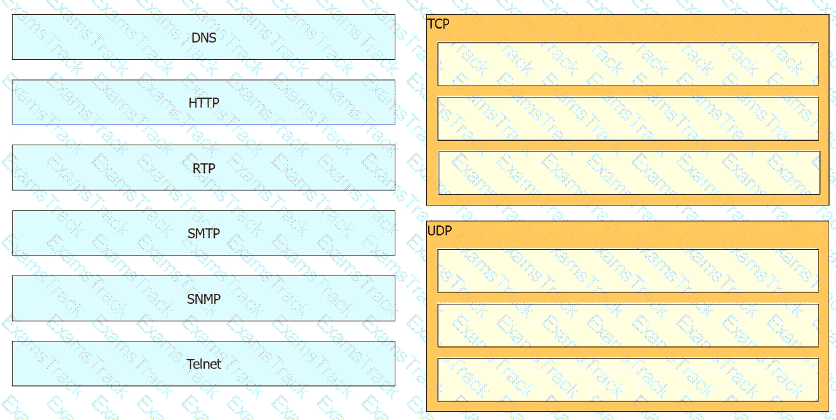
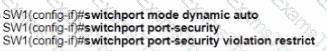
Drag and drop the TCP/IP protocols from the left onto their primary transmission protocols on the right.
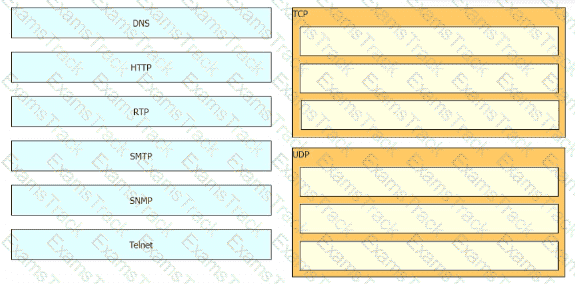
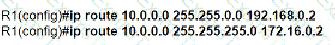
Refer to the exhibit.
A network engineer must configure R1 so that it sends all packets destined to the 10.0.0.0/24 network to R3, and all packets destined to PCI to R2. Which configuration must the engineer implement?
A)
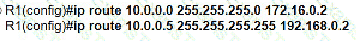
B)
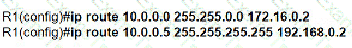
C)
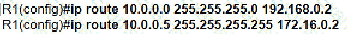
D)
Refer to the exhibit.
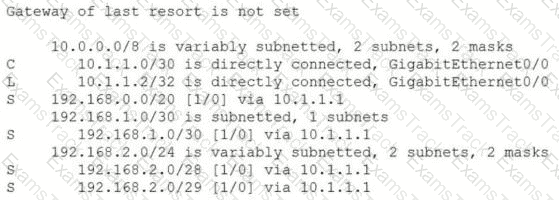
An engineer is checking the routing table in the main router to identify the path to a server on the network. Which route does the router use to reach the server at 192.168.2.2?
Refer to the exhibit.
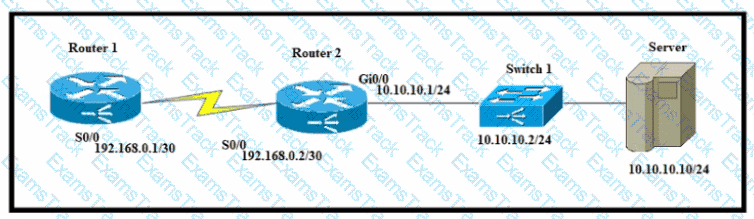
A network engineer must configure router R1 with a host route to the server. Which command must the engineer configure?
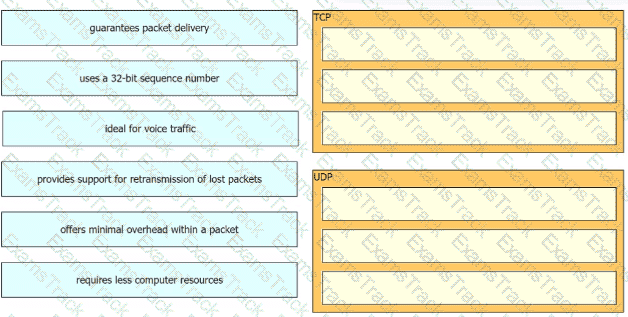
Drag and drop the characteristics of transport layer protocols from the left onto the corresponding protocols on the right.
How does frame switching function on a switch?
Refer to the exhibit.
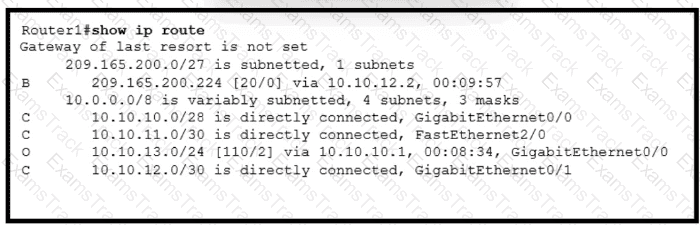
Which action by the router when a packet is sourced from 10.10.10.2 and destined 10.10.10.16?
When a switch receives a frame for an unknown destination MAC address, how is the frame handled?
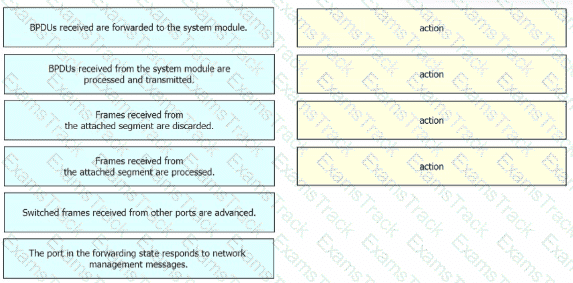
Drag and drop the Rapid PVST+ forwarding state actions from the left to the right. Not all actions are used.
Refer to the exhibit.
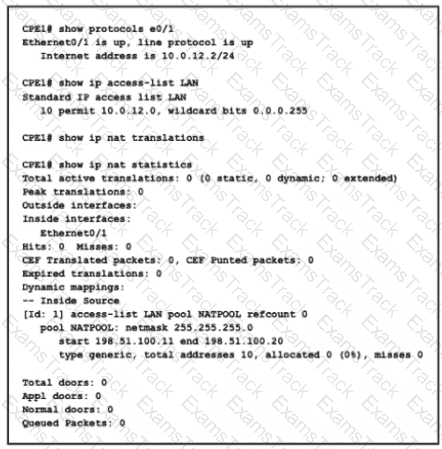
What is the next step to complete the implementation for the partial NAT configuration shown?
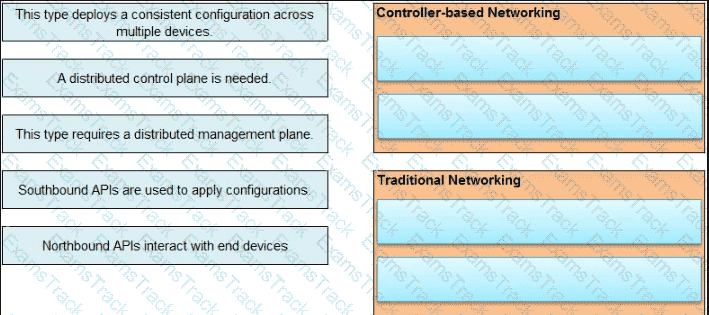
Drag and drop the statements about networking from the left onto the corresponding networking types on the right. Not all statements are used.
Which protocol must be implemented to support separate authorization and authentication solutions for wireless APs?
|
PDF + Testing Engine
|
|---|
|
$52.5 |
|
Testing Engine
|
|---|
|
$40.5 |
|
PDF (Q&A)
|
|---|
|
$34.5 |
Cisco Free Exams |
|---|

|