: 243
You have a Microsoft 365 tenant that uses Microsoft Endpoint Manager for device management. You need to add the phone number of the help desk to the Company Portal app. What should you do?
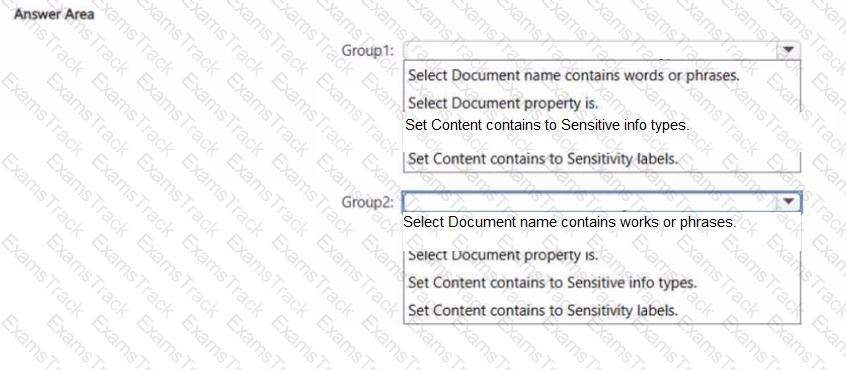
You have a Microsoft 365 E5 subscription that contains two groups named Group1 and Group2. You plan to configure a data loss prevention (DLP) strategy that meets the following requirements:
• Members of Group1 must be prevented from sharing documents that contain credit card numbers.
• Members of Group2 must be prevented from sharing documents that are classified as internal by Microsoft Purview Information Protection.
• The solution must minimize administrative effort
You need to create a DLP policy for each group.
Which condition should you add to each DLP policy rule for each group? To answer, select the appropriate options in the answer
area.
NOTE: Each correct selection is worth one point.
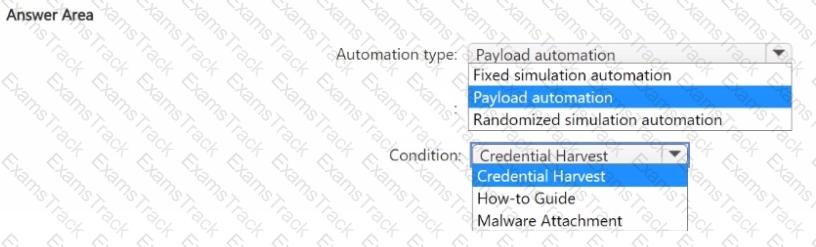
You have a Microsoft 365 E5 subscription that uses Microsoft Defender for Office 365.
You need to automate Attack simulation training for users when a phishing campaign is detected in real-time.
Which type of automation should you use. and which condition should you configure for the Attack simulation training? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft Entra tenant named contoso.com that contains the users shown in the following table.
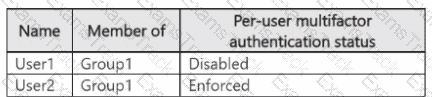
Per-user multifactor authentication is configured to use 131.107.5.0/24 as trusted IPs.
The tenant contains the named locations shown in the following table.
You create a conditional access policy that has the following configurations:
• Users: All users
• Target resources assignment: App1
• Conditions: Include all trusted locations
• Grant access: Require multi-factor authentication
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.

You have the sensitivity labels shown in the following exhibit.
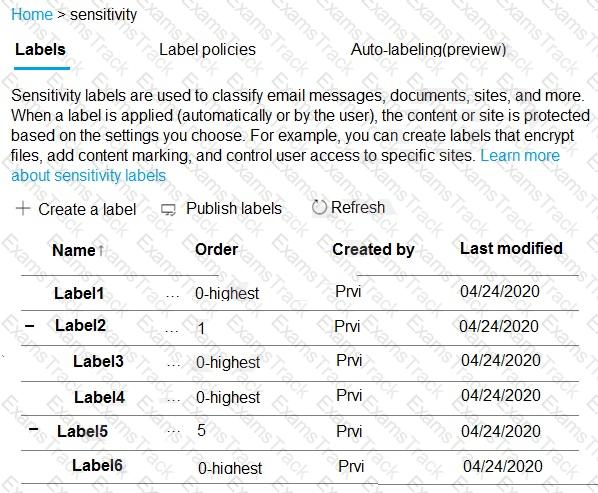
Which labels can users apply to content?
You have a Microsoft 365 E5 subscription and an Azure AD tenant named contoso.com.
All users have computers that run Windows 11, are joined to contoso.com, and are protected by using BitLocker Drive Encryption (BitLocker).
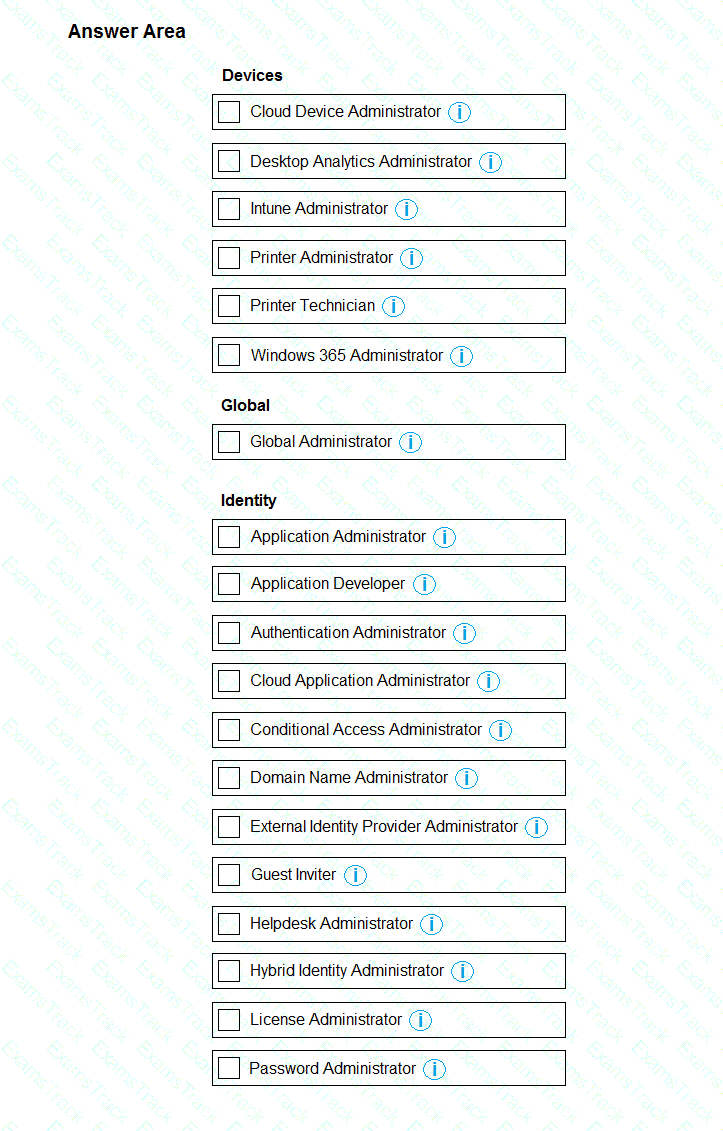
You plan to create a user named Admin1 that will perform following tasks:
• View BitLocker recovery keys.
• Configure the usage location for the users in contoso.com.
You need to assign roles to Admin1 to meet the requirements. The solution must use the principle of least privilege. Which two roles should you assign? To answer, select the appropriate roles in the answer area.
NOTE: Each correct selection is worth one point
You have a Microsoft 365 ES subscription.
You integrate Microsoft Defender for Endpoint with Microsoft Intune.
You need to ensure that devices automatically onboard to Defender for Endpoint when they are enrolled In Intune.
Solution: You create an endpoint detection and response (EDR) policy.
Does this meet the goal?
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
Your network contains an on-premises Active Directory domain named contoso.com. The domain contains the users shown in the following table.
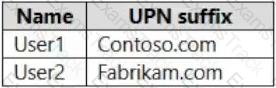
The domain syncs to an Azure AD tenant named contoso.com as shown in the exhibit. (Click the Exhibit tab.)
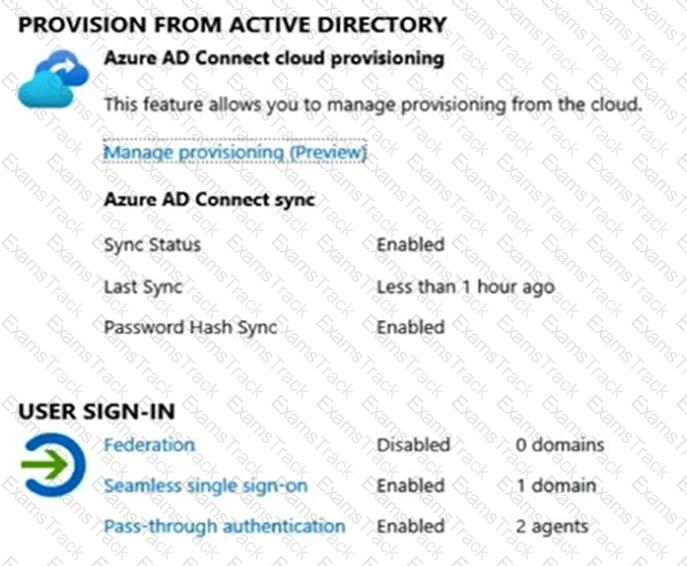
User2 fails to authenticate to Azure AD when signing in as user2@fabrikam.com.
You need to ensure that User2 can access the resources in Azure AD.
Solution: From the on-premises Active Directory domain, you set the UPN suffix for User2 to @contoso.com. You instruct User2 to sign in as user2@contoso.com.
Does this meet the goal?
You have a Microsoft 365 subscription.
From the Microsoft Entra authentication methods policy, you configure the Microsoft Authenticator on companion applications settings as shown in the following exhibit.
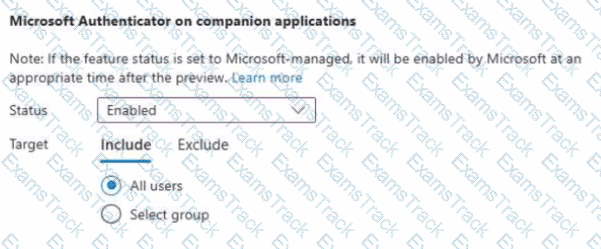
You need to ensure that users can complete the authentication process from their mobile device. What should each user install on their device?
You have a Microsoft 365 E5 subscription.
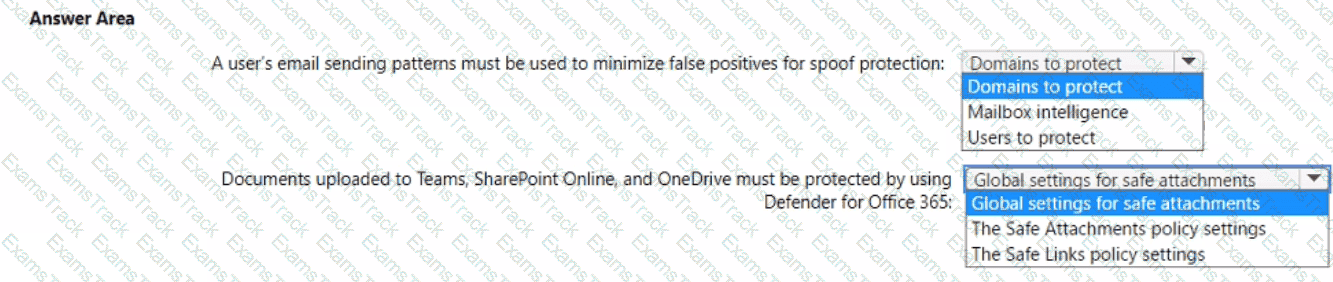
You need to configure Microsoft Defender for Office 365 to meet the following requirements:
• A user ' s email sending patterns must be used to minimize false positives for spoof protection.
• Documents uploaded to Microsoft Teams, SharePoint Online, and OneDrive must be protected by using Defender for Office 365.
What should you configure for each requirement? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
|
PDF + Testing Engine
|
|---|
|
$52.5 |
|
Testing Engine
|
|---|
|
$40.5 |
|
PDF (Q&A)
|
|---|
|
$34.5 |
Microsoft Free Exams |
|---|

|