When a traditional network is transformed to a hierarchical network, the state information in the control plane is reduced so that changes in one area of the network do not result in changes in the routing table on devices half-way around the globe What is a potential trade off in these cases?
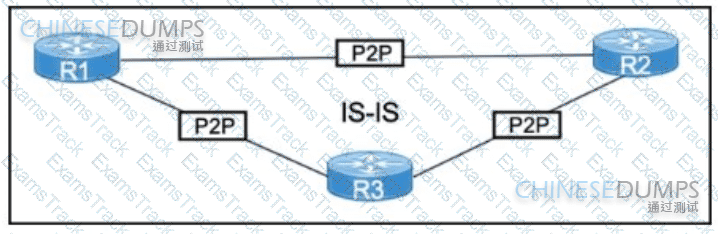
Refer to the exhibit After a network audit a network engineer must optimize the current network convergence time The proposed solution must consider link layer and control plane failures Which solution meets the requirements?
Network designers often segment networks by creating modules for various reasons Sometimes however a network can be unintentionally segmented For instance, if the only way to connect a remote site to a headquarters or regional site is to connect them both to the public Internet the corporate network is now unintentionally segmented Which of the following option can be used to desegment the network in this situation?
During initial preparations to deploy 802 1x for wired access to their network, a company must ensure that the solution complies with existing internal security policies These policies mandate that every Auth C/Auth Z request must be protected by a tunnel which authenticates both server and clients using their PKI AI the same time, the user authentication phase must be independent of the tunnel Which scheme meets the requirements?
Which undesired effect of increasing the jitter compensation buffer is true?
Which two factors must be considered while calculating the RTO? (Choose two . )
What are three examples of solution components of the network infrastructure that help enforce security policy compliance on all devices as they seek to access the network and computing resources, thereby limiting damage from emerging security threats such as viruses, worms, and spyware? (Choose three)
Company XYZ Is running a redundant private WAN network using OSPF as the underlay protocol The current design accommodates for redundancy In the network, but it Is taking over 30 seconds for the network to reconverge upon failure Which technique can be Implemented In the design to detect such a failure in a subsecond?
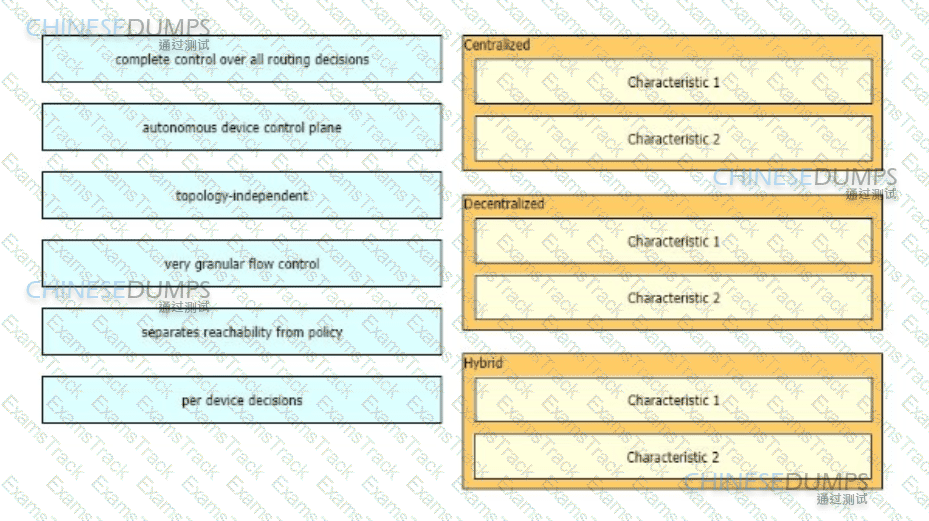
As part of a design solution a consultant needs to describe the trade-offs between different SDN models Drag the characteristics on the left to the correct controller-based network designs on the right in no particular order.
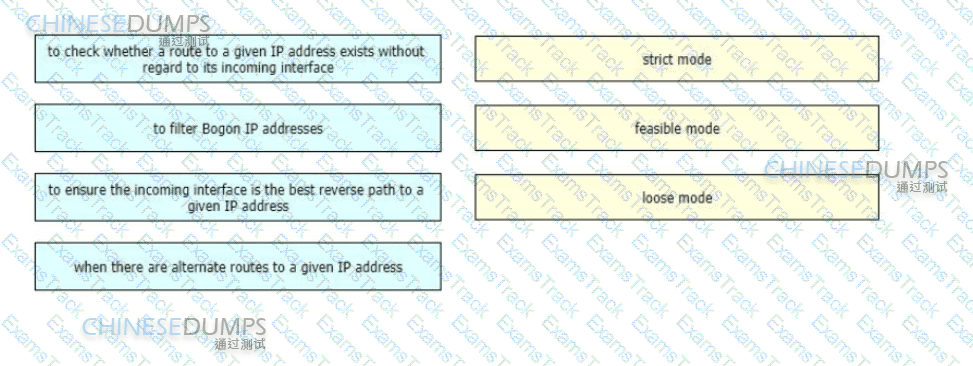
A networking team needs to prevent spoofing attacks They are describing the different uRPF design use cases so they can identify and deploy the optimal mode in various parts of their network
Drag and drop the use cases from the left onto the corresponding uRPF technique on the right Not all options are used
|
PDF + Testing Engine
|
|---|
|
$179.7 |
|
Testing Engine
|
|---|
|
$134.7 |
|
PDF (Q&A)
|
|---|
|
$119.7 |
Cisco Free Exams |
|---|

|