Which service abstracts away the management of the operating system, middleware, and runtime?
Which purpose of a dynamically created tunnel interface on the design of IPv6 multicast services Is true?
A well-executed network design provides improved performance and efficiency, increased security, and reduced downtime and support costs Which feature helps to achieve resilience in the network?
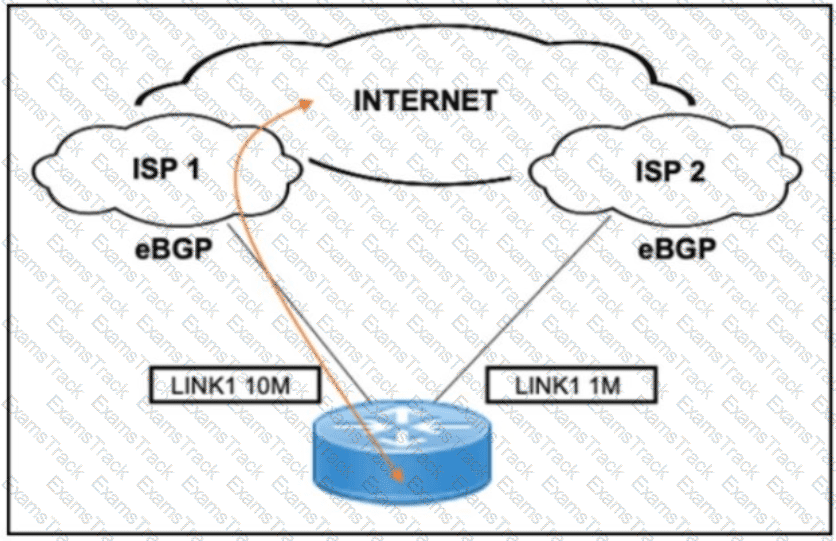
Refer to the exhibit. A customer needs to implement a connectivity model by using one active link for inbound and outbound traffic and a second link for backup. The backup link is low speed and is required only during outages of the primary link. Which design solution should be implemented?
A business wants to centralize servies via VDI technology and to replace remote WAN desktop PCs with thin client-type machines to reduce operating costs Which consideration supports the new business requirement?
A network architect is working on the baseline policies dealing with the use of Infrastructure-as-Code within an IT department, and has been requested to present the plan at the monthly management board meeting. What are two examples of operational aspects of Infrastructure-as-Code that can be highlighted during the presentation? (Choose two.)
Which design element is used to define network performance requirements?
SDN is still maturing Throughout the evolution of SDN which two things will play a key role in enabling a successful deployment and avoiding performance visibility gaps in the infrastructure’ (Choose two.)
A software-defined network can be defined as a network with an API that allows applications to understand and react to the state of the network in near real time A vendor is building an SDN solution that exposes an API to the RIB and potentially the forwarding engine directly The solution provides off-box processes with the capability to interact with the routing table in the same way as a distributed routing process Which SDN framework model does the solution use?
In traditional network design, the network and data center are confined within a single building In this configuration, a router connects the internal and external networks Basic configuration of an access control list within the router controls the traffic that can pass through Which security technique defines the boundary between an internal/trusted network and an external/untrusted network?
|
PDF + Testing Engine
|
|---|
|
$179.7 |
|
Testing Engine
|
|---|
|
$134.7 |
|
PDF (Q&A)
|
|---|
|
$119.7 |
Cisco Free Exams |
|---|

|