Company XYZ has designed their network to run GRE over IPsec on their Internet- based VPN to connect two sites Which IPsec tunneling feature can they enable to optimize the data flow while ensuring that the headers contain no duplicate IP addresses?
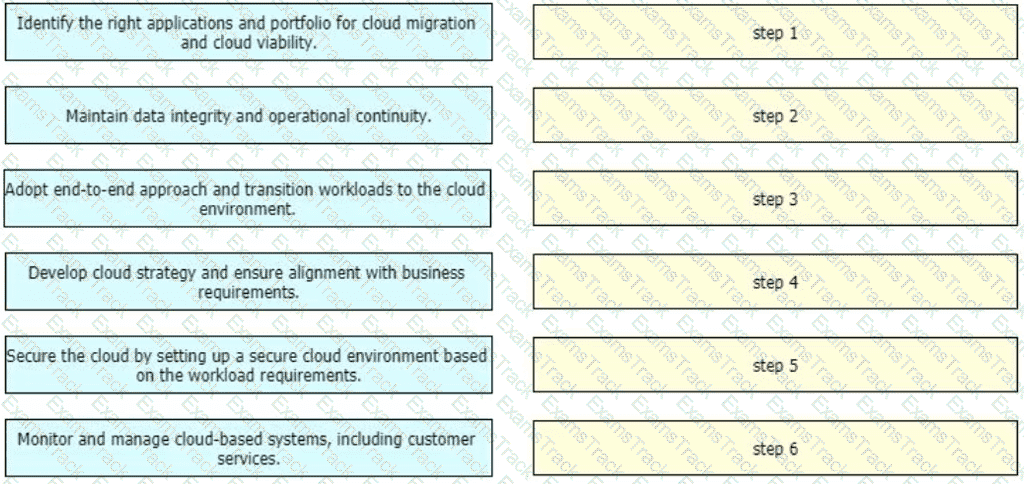
An enterprise wants to migrate an on-premises network to a cloud network, and the design team is finalizing the overall migration process. Drag and drop the options from the left into the correct order on the right.
Company XYZ has two routing domains in their network, EIGRP and OSPF. The company wants to provide full reachability between the two domains by implementing redistribution on a router running both protocols They need to design the redistribution in a way that the OSPF routers will see link costs added to external routes. How must the redistribution strategy be designed for this network?
What is the primary benefit for an organization that dynamically can expand their private cloud capacity by allocating additional compute and/or storage resources using a third-party service provider or partner?
An enterprise wants to provide low-cost delivery of network systems that can be scaled on business demand, followed by an initiative to reduce capital expenses for new IT equipment Which technology meets these goals?
A multinational organization has decided to migrate its business-critical operations to a hybrid cloud solution They are concerned about data governance, particularly regarding data sovereignty, ownership, and locale The company operates in multiple countries with strict data privacy regulations Which solution best ensures compliance with data governance regulations ' ?
Piggybank, a leading financial institution, is planning to migrate its business-critical operations to a hybrid cloud solution A recommendation of the most appropriate security measure to protect sensitive financial data during data transmission must be given to the board of directors Which solution will meet these requirements?
Company XYZ wants to implement an IPS device to detect and block well-known attacks against their network They want a design solution where all packets that are forwarded to the network are checked against a signature database before being allowed through This check must be done with the minimum effect on performance Which design is recommended?
What is the best approach in a large legacy application migration scenario when the goal is to complete the migration in the shortest possible time?
A legacy enterprise is using a Service Provider MPLS network to connect its head office and branches. Recently, they added a new branch to their network. Due to physical security concerns, they want to extend their existing IP CCTV network of the head office to the new branch, without any routing changes in the network. They are also under some time constraints. What is the best approach to extend the existing IP CCTV network to the new branch, without incurring any IP address changes?
|
PDF + Testing Engine
|
|---|
|
$179.7 |
|
Testing Engine
|
|---|
|
$134.7 |
|
PDF (Q&A)
|
|---|
|
$119.7 |
Cisco Free Exams |
|---|

|