An administrator needs to delegate the management of security policies to a dedicated SecOps team. To enforce the principle of least privilege, the administrator assigns the predefined Flow Policy Author role to a user on the team. The user confirms they can create, monitor, and enforce security policies. However, when attempting to build a new application security policy for a set of newly deployed VMs, the user reports they are unable to create a new category to group these VMs. The option is not available in the Prism Central UI. Which statement explains this behavior?
What type of policy would be used to block all traffic between VMs in the category Environment:Sandbox and VMs in the category Environment:Production?
How can the administrator discover the root cause of the issue?
An administrator has configured two VPCs with overlapping externally routable prefixes (ERPs). The two VPCs are associated to separate external networks that are part of the same physical routing domain. What outcome should the administrator expect?
Which step is required before placing the Flow Network Security software bundle on a local web server?
Refer to Exhibit:
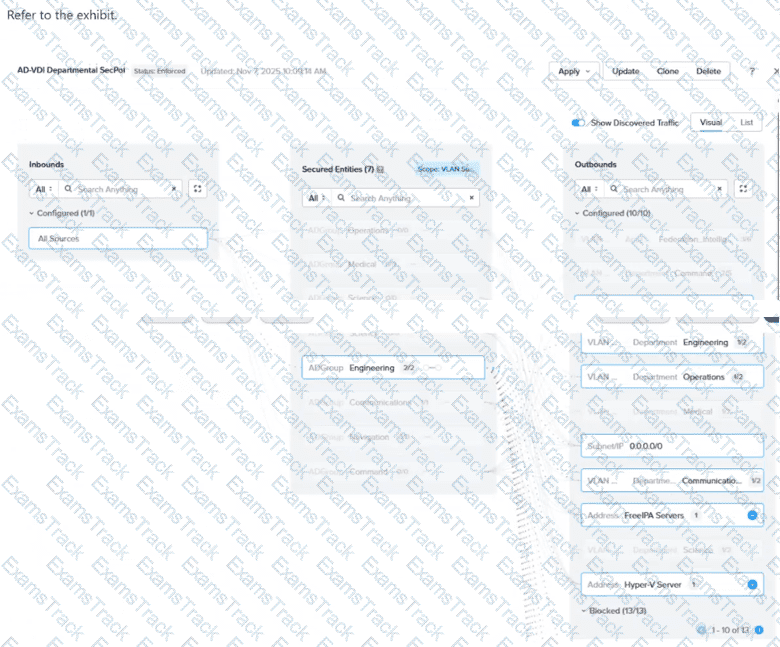
In the AD-VDI Departmental SecPol policy shown in the exhibit, ADGroup: Engineering is configured as a secured entity in a VDI Security Policy. Prism Central shows 2 / 2 active sessions under this group, but the administrator confirms that three Engineering users are currently logged in to persistent VDI desktops. The third user's VM shows no ADGroup assignment in its VM details in Prism Central, even after the user has successfully logged in. All three users are members of the same AD group, and the Domain Controller event logs confirm a successful interactive login for the third user. Which condition explains why the third user's VM is not being assigned the ADGroup: Engineering category?
Users have recently reported intermittent connectivity issues and slower-than-usual application performance for a Nutanix cluster to an administrator. The administrator needs to identify the root cause of these issues by analyzing the health of the infrastructure components. What action should the administrator take first to diagnose the root cause of the problem?
An administrator has a requirement to capture application flow data for a policy in Monitor mode and export those events to an external SIEM for correlation with other logs. Which two actions are required to achieve this? (Choose two.)
Refer to Exhibit:
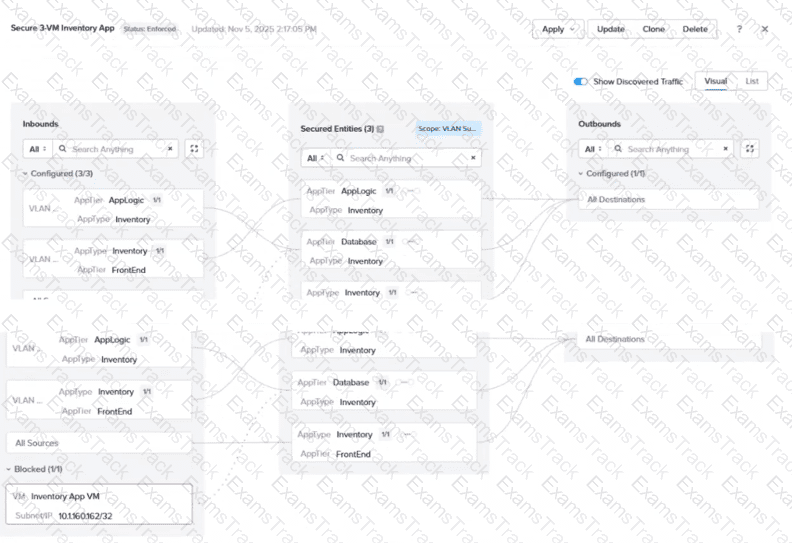
An administrator is reviewing an enforced security policy "Secure 3-VM Inventory App", as shown in the exhibit. The policy's inbound rules are configured to allow traffic from specific sources to each tier of the application. The visualization shows one blocked traffic flow. Based on the information presented in the exhibit, which statement best describes this behavior?
An enterprise has deployed a VPC called FinanceVPC using Nutanix Flow Virtual Networking. The Finance team needs the following connectivity: Internal servers in the VPC must reach an on-premises corporate data-center via a point-to-point encrypted link. Some servers in the VPC must also access the public internet with source NAT and receive inbound access via floating IPs. The corporate network uses overlapping IP space with other VPCs in the environment, so address translation is necessary for those workloads. The networking design must support routing via BGP for future site expansions and provide low-latency north-south connectivity. Which actions should the administrator take to satisfy this requirement?
|
PDF + Testing Engine
|
|---|
|
$49.5 |
|
Testing Engine
|
|---|
|
$37.5 |
|
PDF (Q&A)
|
|---|
|
$31.5 |
Nutanix Free Exams |
|---|

|