Which policy mode blocks all traffic that is not explicitly allowed by the policy?
An administrator has been tasked with configuring virtual switches and setting the appropriate MTU size for a Nutanix cluster to optimize network performance. The cluster needs to support high-throughput traffic between VMs and ensure compatibility with external networks. The administrator needs to configure the virtual switches and MTU size to enable jumbo frames while ensuring that all nodes and network components are properly aligned to prevent packet loss or fragmentation. What is the first step to configure the virtual switches and MTU size in a Nutanix cluster for optimal network performance?
An administrator is responsible for managing user access to a Nutanix cluster... configure custom user roles... What is the first step in configuring and managing user roles for a Nutanix cluster?
What is the role of the Network Controller in Flow Virtual Networking?
Which policy is used to isolate a compromised VM in the most efficient way possible?
Which action allows an administrator to reuse a single existing policy in a different scope?
Which statement accurately describes the behavior of a Flow Network Security policy operating in Monitor mode?
An administrator has deployed a microsegmentation policy in Nutanix Flow that allows certain VM traffic based on Active Directory (AD) user group membership. Users in a specific AD group report they are unable to access the VMs, while other users can connect without issues. The administrator suspects the problem is related to identity-based policy mapping. What should the administrator do to troubleshoot and resolve the access issue related to the identity-based policy?
Exhibit:
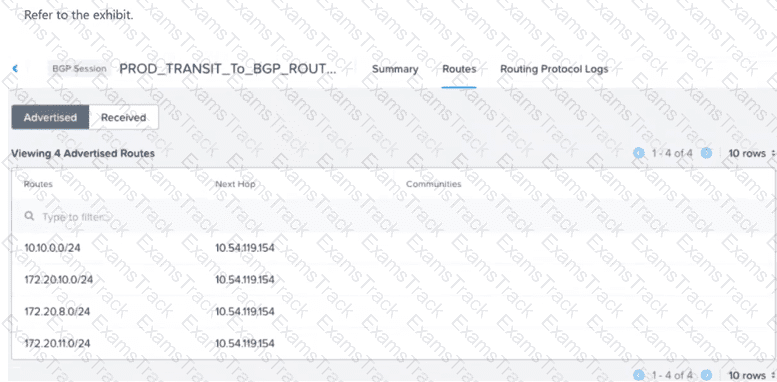
A VM with IP address 172.20.9.5 resides on a subnet with CIDR 172.20.9.0/24. The VPC is successfully peered via BGP with an external router... External networks outside the VPC are unable to reach the VM. What configuration change should be made to enable reachability for the VM?
An administrator sets up a VPN between two Nutanix VPCs in different Availability Zones. After deployment, the VPN tunnel shows as Up, but traffic between the VPCs is not flowing. Which configuration step is most likely missing?
|
PDF + Testing Engine
|
|---|
|
$49.5 |
|
Testing Engine
|
|---|
|
$37.5 |
|
PDF (Q&A)
|
|---|
|
$31.5 |
Nutanix Free Exams |
|---|

|