You are asked to configure 802.1X on an EX Series switch port that connects to a downstream switch with several devices attached. You must ensure that the first device is authenticated while all subsequent devices are permitted.
What will accomplish this request?
You are deploying IP phones in your enterprise networks. When plugged in. the IP phones must automatically be provided with their geographic location details by the EX Series switches.
In this scenario, which protocol should be used to enable this behavior?
Which statement about LLDP and LLDP-MED operations on EX Series devices is correct?
Exhibit.
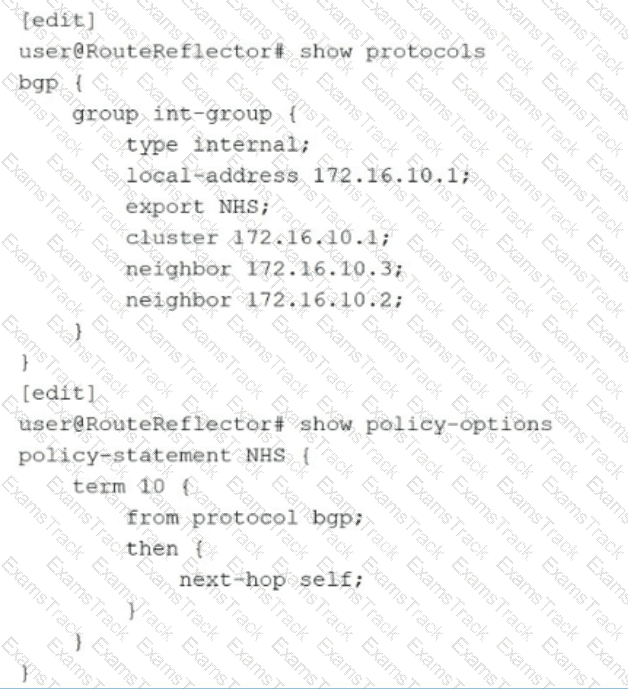
You have determined that traffic in your network is being routed through your route reflector instead of using the optimal path. Referring to the exhibit, what are two configuration changes on the route reflector that would solve the problem? (Choose two.)
Exhibit.
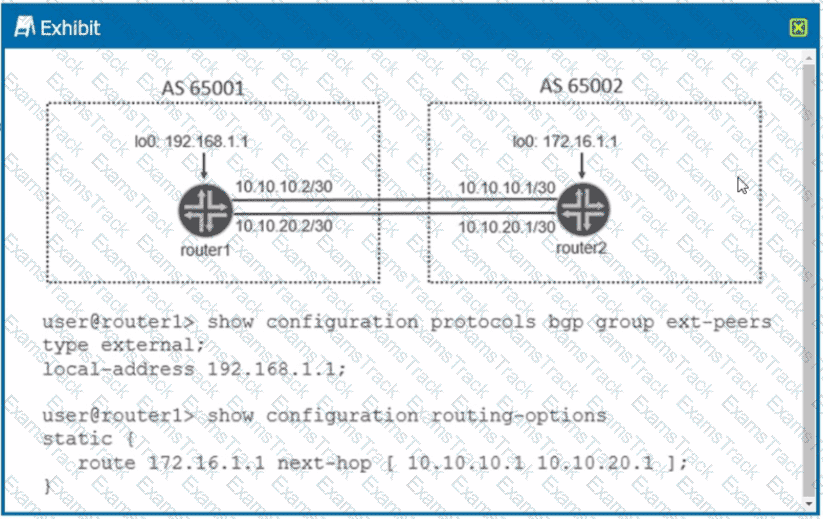
Referring to the exhibit, what is required for the BGP peering to establish?
Exhibit
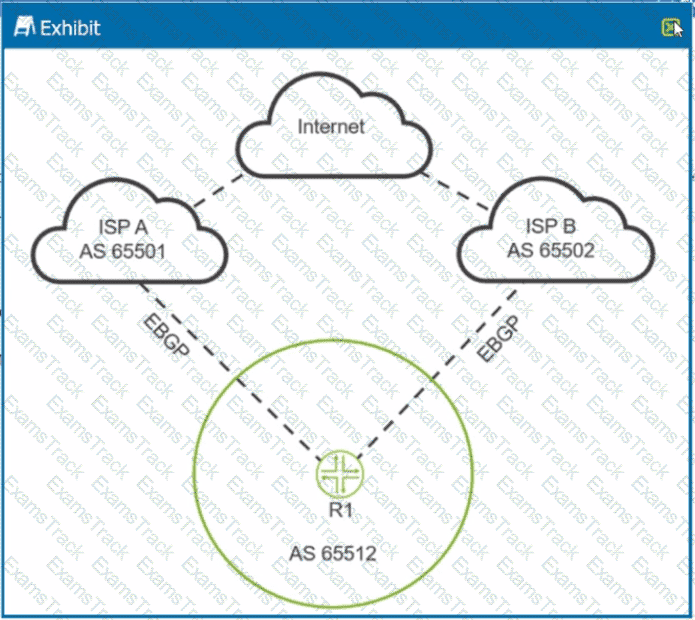
You are receiving the same BGP Internet routes on R1 from both upstream ISPs. You are asked to load-balance traffic destined to the Internet across both ISPs.
Referring to the exhibit, which BGP solution should you use?
Exhibit
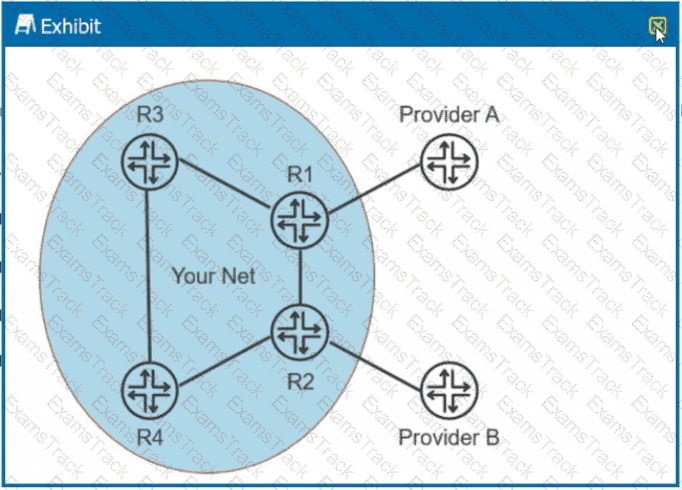
Your network receives the full Internet BGP routing table from two different ISPs. You want your local routers to use Provider A to forward all Internet traffic as long as Provider A is available.
Referring to the exhibit, which two actions would satisfy this requirement? (Choose two.)
Which two statements are correct about multicast routing tables? (Choose two.)
When configuring OSPF. what is the purpose of adding the secondary command to an OSPF interface?
Which two statements are correct about EVPN/VXLAN deployments? (Choose two.)
|
PDF + Testing Engine
|
|---|
|
$49.5 |
|
Testing Engine
|
|---|
|
$37.5 |
|
PDF (Q&A)
|
|---|
|
$31.5 |
Juniper Free Exams |
|---|

|