A company wants HPE Aruba Networking ClearPass Policy Manager (CPPM) to periodically poll Microsoft Endpoint Manager (formerly Intune) for attributes about its managed clients.
What should you do on ClearPass to permit this integration?
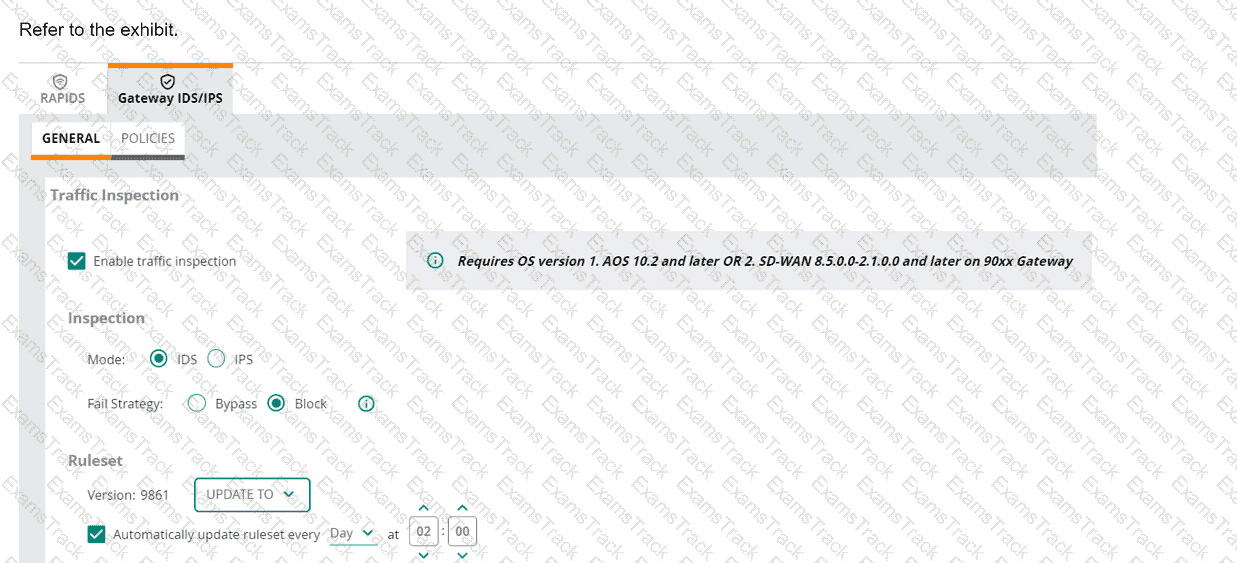
(Note that the HPE Aruba Networking Central interface shown here might look slightly different from what you see in your HPE Aruba Networking Central
interface as versions change; however, similar concepts continue to apply.)
An HPE Aruba Networking 9x00 gateway is part of an HPE Aruba Networking Central group that has the settings shown in the exhibit. What would cause the
gateway to drop traffic as part of its IDPS settings?
HPE Aruba Networking Central displays an alert about an Infrastructure Attack that was detected. You go to the Security > RAPIDS events and see that the attack
was " Detect adhoc using Valid SSID. "
What is one possible next step?
Refer to the exhibit.
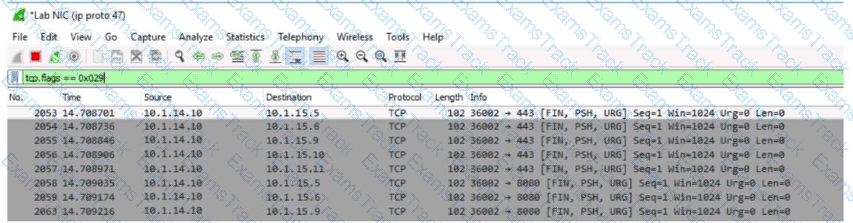
You are reviewing packets in Wireshark. The capture shows traffic from source IP address 10.1.14.10 to several destinations in the 10.1.15.0/24 network. The packets use TCP flags FIN, PSH, and URG together.
What can you interpret from the packets that you see here?
What is one use case that companies can fulfill using HPE Aruba Networking ClearPass Policy Manager ' s (CPPM ' s) Device Profiler?
A company has AOS-CX switches. The company wants to make it simpler and faster for admins to detect denial of service (DoS) attacks, such as ping or ARP floods, launched against the switches.
What can you do to support this use case?
A company is using HPE Aruba Networking ClearPass Device Insight (CPDI) (the standalone application). In the CPDI security settings, Security Analysis is On, the Data Source is ClearPass Device Insight, and Enable Posture Assessment is On. You see that a device has a Risk Score of 90.
What can you know from this information?
A company has a variety of HPE Aruba Networking solutions, including an HPE Aruba Networking infrastructure and HPE Aruba Networking ClearPass Policy Manager (CPPM). The company passes traffic from the corporate LAN destined to the data center through a third-party SRX firewall. The company would like to further protect itself from internal threats. What is one solution that you can recommend?
You are setting up user-based tunneling (UBT) between access layer AOS-CX switches and AOS-10 gateways. You have selected reserved (local) VLAN mode.
Tunneled devices include IoT devices, which should be assigned to:
Roles: iot on the switches and iot-wired on the gateways
VLAN: 64, for which the gateways route traffic.
IoT devices connect to the access layer switches ' edge ports, and the access layer switches reach the gateways on their uplinks.
Where must you configure VLAN 64?
A company has Aruba APs that are controlled by Central and that implement WIDS. When you check WIDS events, you see a " detect valid SSID misuse " event. What can you interpret from this event, and what steps should you take?
|
PDF + Testing Engine
|
|---|
|
$49.5 |
|
Testing Engine
|
|---|
|
$37.5 |
|
PDF (Q&A)
|
|---|
|
$31.5 |
HP Free Exams |
|---|

|