You are deploying a virtual Data Collector for use with HPE Aruba Networking ClearPass Device Insight (CPDI). You have identified VLAN 101 in the data center
as the VLAN to which the Data Collector should connect to receive its IP address and connect to HPE Aruba Networking Central.
Which Data Collector virtual ports should you tell the virtual admins to connect to VLAN 101?
Refer to the Exhibit:
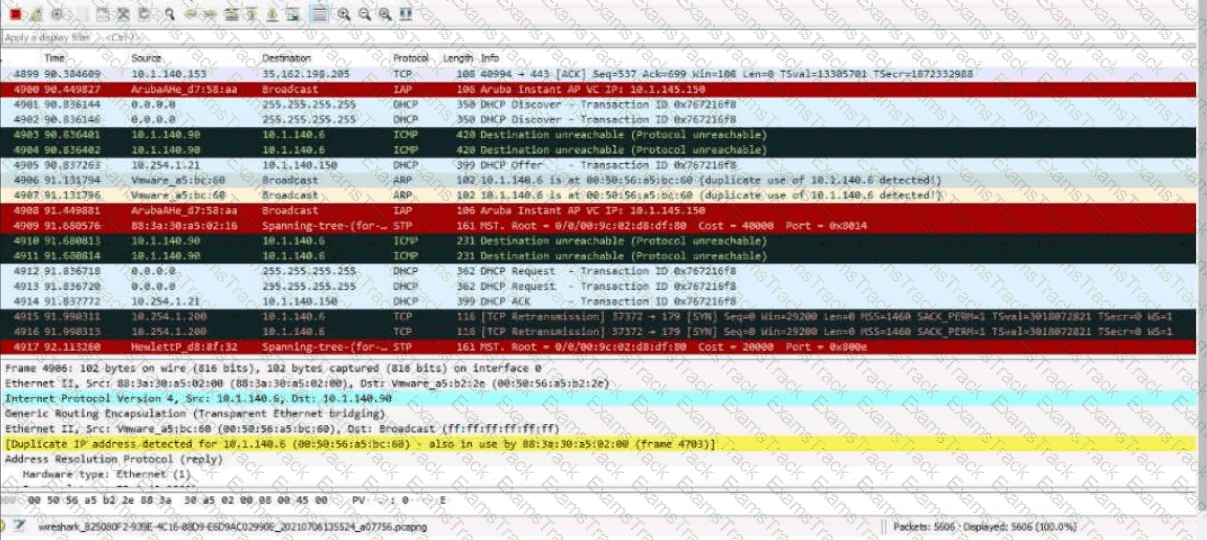
These packets have been captured from VLAN 10. which supports clients that receive their IP addresses with DHCP.
What can you interpret from the packets that you see here?
These packets have been captured from VLAN 10, which supports clients that receive their IP addresses with DHCP. What can you interpret from the packets that you see here?
You manage AOS-10 APs with HPE Aruba Networking Central. A role is configured on these APs with the following rules:
Allow UDP on port 67 to any destination
Allow any to network 10.1.6.0/23
Deny any to network 10.1.0.0/16 + log
Deny any to network 10.0.0.0/8
Allow any to any destination
You add this new rule immediately before rule 2:
Deny SSH to network 10.1.4.0/23 + denylist
What happens when a client assigned to this role sends SSH traffic to 10.1.11.42?
You are setting up policy rules in HPE Aruba Networking SSE. You want to create a single rule that permits users in a particular user group to access multiple applications. What is an easy way to meet this need?
You have installed an HPE Aruba Networking Network Analytic Engine (NAE) script on an AOS-CX switch to monitor a particular function.
Which additional step must you complete to start the monitoring?
You have enabled " rogue AP containment " in the Wireless IPS settings for a company’s HPE Aruba Networking APs. What form of containment does HPE Aruba Networking recommend?
A company uses both HPE Aruba Networking ClearPass Policy Manager (CPPM) and HPE Aruba Networking ClearPass Device Insight (CPDI).
What is one way integrating the two solutions can help the company implement Zero Trust Security?
A company uses HPE Aruba Networking ClearPass Device Insight (CPDI) as the standalone application.
How does CPDI handle devices that it cannot classify with user rules, system rules, or MAC range classifiers?
You have created a Web-based Health Check Service that references a posture policy. You want the service to trigger a RADIUS change of authorization (CoA) when a client receives a Healthy or Quarantine posture. Where do you configure those rules?
Assume that an AOS-CX switch is already implementing DHCP snooping and ARP inspection successfully on several VLANs.
What should you do to help minimize disruption time if the switch reboots?
|
PDF + Testing Engine
|
|---|
|
$49.5 |
|
Testing Engine
|
|---|
|
$37.5 |
|
PDF (Q&A)
|
|---|
|
$31.5 |
HP Free Exams |
|---|

|