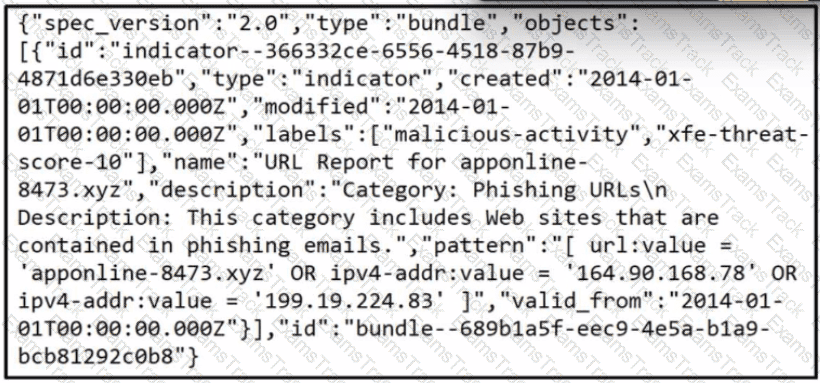
Refer to the exhibit.
What does the exhibit indicate?
Refer to the exhibit.
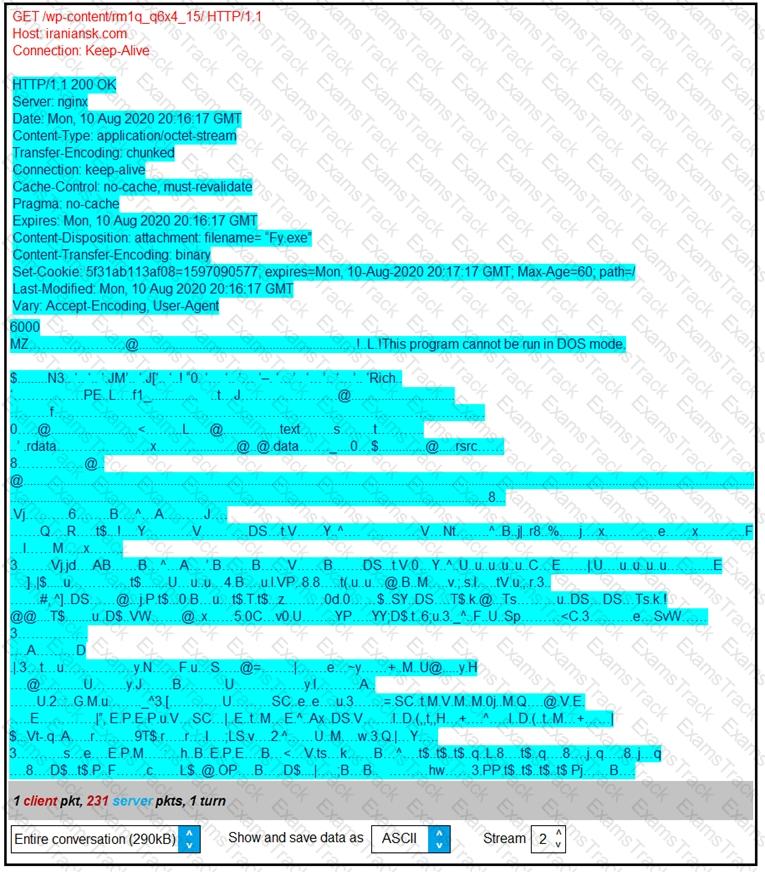
According to the Wireshark output, what are two indicators of compromise for detecting an Emotet malware download? (Choose two.)
During an overnight shift, a cybersecurity team at a global trading firm detects irregular activity The network intrusion system flags an encrypted traffic spike from high-value transaction servers to an anonymous Tor exit node Simultaneously, internal surveillance tools report unusual database queries and access patterns resembling exfiltration techniques Which focused action should the team take first to analyze and address these potential security threats?
A threat hunter must analyze the threat intelligence report on APT29 and identify whether the threat actor is on the Windows machines of the customer network. According to the report the user executes a malicious file on the victim machine that establishes a C? connection over port 53 Afterward, the attacker uses a CI.I to stage and exfiltrate business data. Which two types of logs enable the threat hunter to accomplish the task? (Choose two.)
Snort detects traffic that is targeting vulnerabilities in files that belong to software in the Microsoft Office suite. On a SIEM tool, the SOC analyst sees an alert from Cisco FMC. Cisco FMC is implemented with Snort IDs. Which alert message is shown?
During a recent incident response investigation, several suspicious network connections originating from a specific host were identified. The host was quickly isolated and the machine was rebuilt During the post mortem, it became clear that there was unpreparedness regarding network artifacts necessitating adjustments to the playbooks to address this data from multiple sources must be correlated. Which two sources should be prioritized for data gathering? (Choose two.)
A scanner detected a malware-infected file on an endpoint that is attempting to beacon to an external site. An analyst has reviewed the IPS and SIEM logs but is unable to identify the file’s behavior. Which logs should be reviewed next to evaluate this file further?
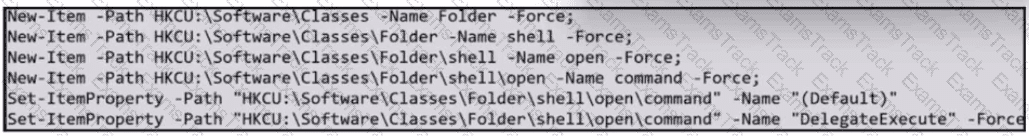
Refer to the exhibit.
Which two actions should be taken as a result of this information? (Choose two.)
Refer to the exhibit.

A security analyst is reviewing alerts from the SIEM system that was just implemented and notices a possible indication of an attack because the SSHD system just went live and there should be nobody using it. Which action should the analyst take to respond to the alert?
|
PDF + Testing Engine
|
|---|
|
$52.5 |
|
Testing Engine
|
|---|
|
$40.5 |
|
PDF (Q&A)
|
|---|
|
$34.5 |
Cisco Free Exams |
|---|

|