Sub-interfaces can be created on GE0/0/1 of a firewall. The sub-interfaces can be added to different VLANs, but cannot be added to security zones.
Which of the following problems cannot be solved using PKI?
Huawei Firewall only supports the inter-domain persistent connection function for TCP packets.
The trigger authentication method for firewall access user authentication does not include which of the following?
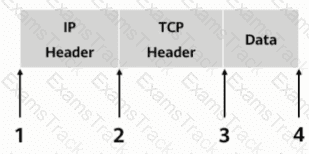
As shown, in transmission mode, which of the following locations should the AH header be inserted in?
In cases where some configurations alter existing session table entries and want them to take effect immediately, you can regenerate the session table by clearing the session table information. All session table information can be cleared by executing the _____firewall session table command.
Information security aims to protect data in hardware, software, and their systems on information networks to prevent data damage, tampering, or breach due to occasional or malicious reasons and ensure proper system running and non-stop information services.
Digital envelope technology means that the sender uses the receiver's public key to encrypt the data, and then sends the ciphertext to the receiver
HTTPS introduces the TLS layer based on HTTP to provide identity authentication, encryption, and integrity check for data transmission.
Which of the following statements is correct about security zones on a Huawei firewall?
|
PDF + Testing Engine
|
|---|
|
$49.5 |
|
Testing Engine
|
|---|
|
$37.5 |
|
PDF (Q&A)
|
|---|
|
$31.5 |
Huawei Free Exams |
|---|

|