Which of the following statements are correct about the status of the firewall VGMP group?
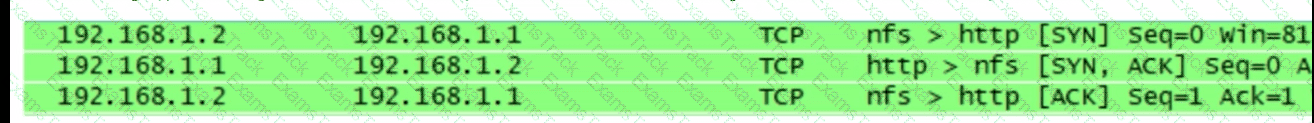
As shown in the figure, packet obtaining software is used to obtain some packets on a terminal. Which of the following statements is correct about the obtained packet information?
What is correct in the following description of Security Alliance in IPSec?
There are two ways to set up an IPSec SA
When using passive mode to establish an FTP connection, the control channel uses port 20 and the data channel uses port 21.
In asymmetric encryption algorithms, only public keys can be used to encrypt data, and private keys are used to decrypt data. This process is irreversible.
Please classify the following security defenses into the correct classification.

When logging in to the web UI through HTTPS, you need to specify a local certificate issued by a CA that the web browser trusts for the HTTPS client on the device. Because the web browser can verify the local certificate, this approach avoids malicious attacks and ensures secure logins of administrators.
3-tuple NAT allows external devices to proactively access internal PCs through translated addresses and ports. Even if no security policy is configured on the firewall, the firewall allows such access packets to pass through.
While working for a company, Tom receives an email with an attachment. Which of the following operations is correct?
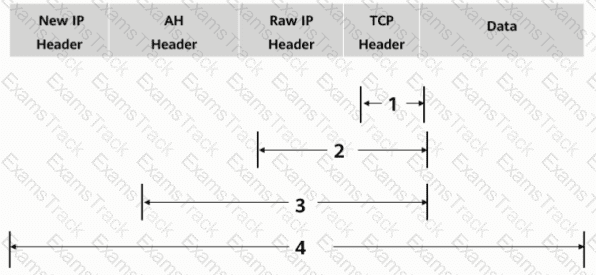
As shown in the figure, what is the authentication range of the AH protocol in tunnel mode?
|
PDF + Testing Engine
|
|---|
|
$49.5 |
|
Testing Engine
|
|---|
|
$37.5 |
|
PDF (Q&A)
|
|---|
|
$31.5 |
Huawei Free Exams |
|---|

|