When IKEv1 negotiation phase 1 uses the aggressive mode, only three messages are used. Which of the following is the function of message 3?
IPS signatures describe the characteristics of attack behaviors on the network. The firewall detects and defends against attacks by comparing data flows with IPS signatures.
The trigger modes of the built-in Portal authentication in the firewall include pre-authentication and ____ authentication[fill in the blank]*
Which of the following packets is controlled by a firewall's security policy by default?
The shard cache technology will wait for the arrival of the first shard packet, and then reassemble and decrypt all the packets, and then do subsequent processing by the device to ensure that the session can proceed normally in some application scenarios.
Which layer of data packets does a packet filtering firewall check?
Which of the following is not an application scenario for PKI?
Which of the following descriptions about the heartbeat interface is wrong ( )?
Which of the following statements is incorrect about DoS attacks?
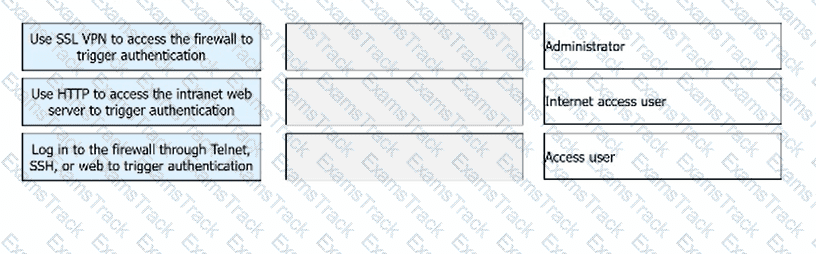
Match the following user categories and authentication modes.
|
PDF + Testing Engine
|
|---|
|
$49.5 |
|
Testing Engine
|
|---|
|
$37.5 |
|
PDF (Q&A)
|
|---|
|
$31.5 |
Huawei Free Exams |
|---|

|