A playbook is configured with two actions: terminate process and isolate device. The terminate process action fails because the process is protected by Windows. What is the expected behavior for the second action, isolate device? (Choose one answer)
Which two statements correctly describe the IoT probing process on FortiEDR? (Choose two answers)
Refer to the Exhibit:
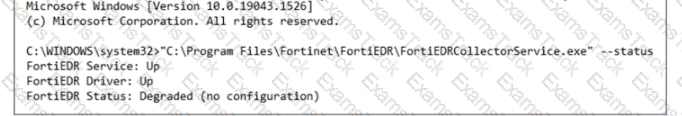
Based on the FortiEDR status output shown in the exhibit, what are two reasons for the degraded state? (Choose two answers)
Refer to the Exhibit:
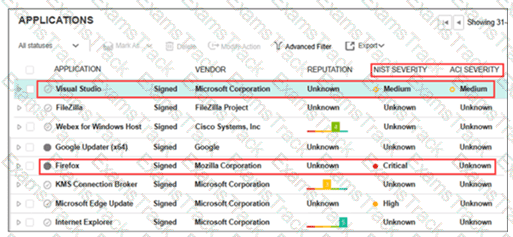
A FortiEDR analyst is prioritizing response efforts. One application has a vulnerability score of Critical but an Unknown ACI rating, while another has a Medium vulnerability score with active ACI evidence of adversary targeting. Which application must be addressed first? (Choose one answer)
A company requires a global communication policy for a FortiEDR multi-tenant environment. Which recommendation must you make? (Choose one answer)
A collector attempts to access a known malicious website. FortiEDR is configured for eXtended detection with FortiAnalyzer. What two roles does Fortinet Cloud Services (FCS) perform in this process? (Choose two answers)
What action does an on-premises reputation server take when it receives a hash request that is not found in its local database? (Choose one answer)
Refer to the exhibit.
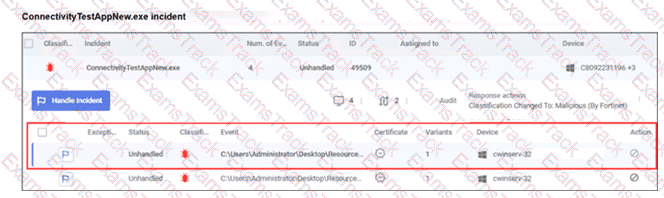
What observation can you make about the ConnectivityTestAppNew.exe incident? (Choose one answer)
You are asked to configure a query to run every 15 minutes, automatically searching for specific registry modifications across all endpoints. Which FortiEDR feature must you configure? (Choose one answer)
|
PDF + Testing Engine
|
|---|
|
$49.5 |
|
Testing Engine
|
|---|
|
$37.5 |
|
PDF (Q&A)
|
|---|
|
$31.5 |
Fortinet Free Exams |
|---|

|