A developer company recently implemented a testing environment based on Linux operating system. The company needs a technology solution that produces tracing and filtering capabilities in the Linux kernel. Which technology meets these requirements without modifying the kernel source code?
An agricultural company wants to enhance the cybersecurity posture by implementing a defense-in-depth strategy to protect against polymorphic malware threats. Currently, the company’s security infrastructure relies solely on a stateful traditional edge firewall that does not provide adequate protection against malware variants. Which technology must be added to the company’s security architecture to achieve the goal?
A product manager is focused on maintaining the security integrity of a microservice-based application as new features are developed and integrated. To ensure that known software vulnerabilities are not introduced into the product, it is crucial to implement a robust application security technique. The technique must be applied during the build phase of the software development lifecycle, which allows the team to proactively identify and address vulnerability risks before deployment. Which application security technique must be applied to accomplish the goal?
Refer to the exhibit.
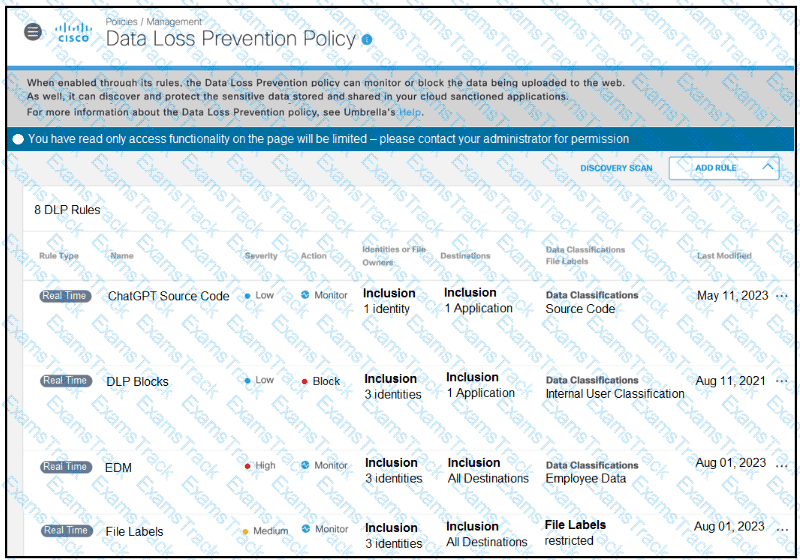
A software developer noticed that the application source code had been found on the internet. To avoid such an incident from happening again, the developer applied a DLP policy to prevent from uploading source code into generative AI tool like ChatGPT. When testing the policy, the developer noticed that it is still possible for the source code to be uploaded. Which action must the developer take to prevent this issue?
A legal services company wants to prevent remote employees from accessing personal email and social media accounts while using corporate laptops. Which security solution enforces the policy?
A manufacturing company experienced a security breach that resulted in sales data being compromised. An engineer participating in the investigation must identify who logged into the sales system during the affected period. Which approach must be used to gather the information?
An IT company experienced the spread of malicious content between user endpoints, which impacted business critical resources. The company wants to implement a solution to control communication between individual endpoints on the network. Which approach achieves the goal?
|
PDF + Testing Engine
|
|---|
|
$52.5 |
|
Testing Engine
|
|---|
|
$40.5 |
|
PDF (Q&A)
|
|---|
|
$34.5 |
Cisco Free Exams |
|---|

|