A financial company is focused on proactively protecting sensitive data stored on the devices. The company recognizes the potential risks associated with lost or stolen devices and they want a solution to ensure that if unauthorized user access the device, the data it contains is not accessible or misused. The solution includes implementing a strategy that renders data unreadable without user authentication. Which solution meets the requirement?
A financial company uses a remote access solution that directs all traffic over a secure tunnel. The company recently received some large ISP bills from the headquarter location. According to traffic analysis during the investigation, most of the network traffic was due to employees spending a lot of time on video conferences provided by a SaaS collaboration company. What must the company modify to reduce the cost without negatively impacting security or employee experience?
An IT company operates an application in a SaaS model. The administrative tasks, such as customer onboarding, within the application must be restricted to users who are on the corporate network where admins can access those functions via a web browser or a smartphone application. Which application technology must be used to provide granular control based on function?
A manufacturing company implemented IoT devices throughout their smart factory and needs a security solution that meets these requirements:
Protect IoT devices from network-based attacks.
Visibility into communication patterns.
Anomaly detection for IoT traffic.
Which firewall technology or feature should be recommended?
Refer to the exhibit.
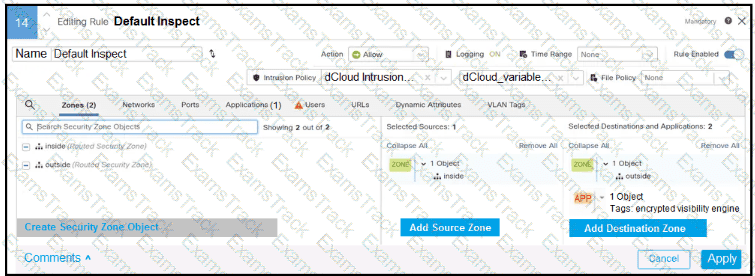
In addition to SSL decryption, which firewall feature allows malware to be blocked?
A global hotel chain is using Cisco ISE and Cisco switches to manage the network. The hotel company wants to enhance network security by segmenting users and endpoints. The company must ensure that devices within the same VLAN cannot communicate with each other. The goal is to prevent cross-communication without the use of dynamic access control lists. Which action must be taken using Cisco ISE to meet the requirement?
After a recent security breach, a financial company is reassessing their overall security posture and strategy to better protect sensitive data and resources. The company already deployed on-premises next-generation firewalls at the network edge for each branch location. Security measures must be enhanced at the endpoint level. The goal is to implement a solution that provides additional traffic filtering directly on endpoint devices, thereby offering another layer of defense against potential threats. Which technology must be implemented to meet the requirement?
An employee of a pharmaceutical company accidentally checked in code that contains AWS secret keys to a public GitHub repository, which exposes production resources to attackers. Which mitigation strategy must a security engineer recommend to prevent future reoccurrence?
What does watermarking AI generated content prevent?
What is a use for AI in securing network infrastructure?
|
PDF + Testing Engine
|
|---|
|
$52.5 |
|
Testing Engine
|
|---|
|
$40.5 |
|
PDF (Q&A)
|
|---|
|
$34.5 |
Cisco Free Exams |
|---|

|