You wish to ensure that all emails to an external partner are sent over a secure connection. What should you do?
What are the three default methods available in Recipient Verification to verify that a recipient mailbox exists?
Pick the 3 correct responses below.
Refer to the exhibit below to see the interface used in this scenario.
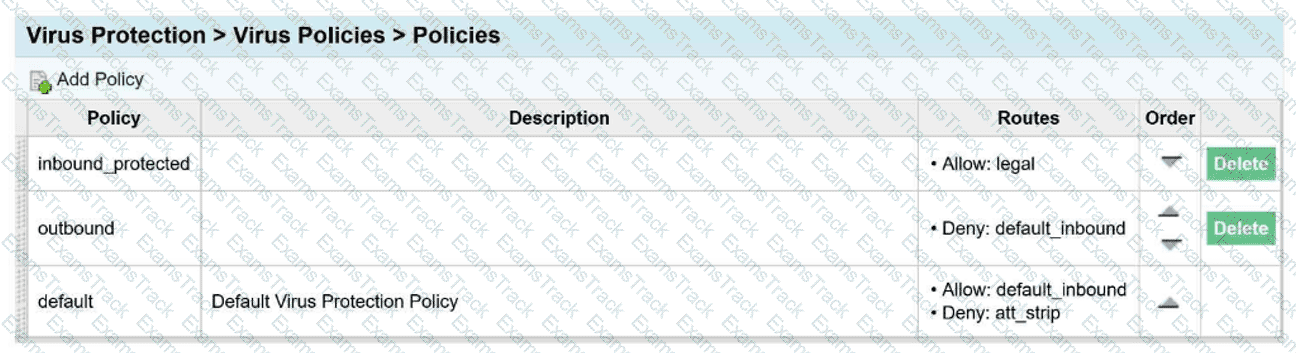
An email arrives inbound to the protection server, it is going to a single recipient and belongs
to the legal and default_inbound policy routes.
Which of the following is true regarding the virus policies?
The Abuse Mailbox event source was working in Cloud Threat Protection, but is now showing red under status and is no longer processing emails. After editing the source and clicking “Validate Source,” you receive the error “Unable to validate mailbox.” What is the likely cause of this error?
During the configuration of an alert profile, which option is specifically required to ensure alerts are delivered to the appropriate individuals?
In the context of email authentication, what is added to the headers of an email message that includes a selector and a hash of the values of selected message headers?
Can a new email digest be generated for every email which enters quarantine?
How does Proofpoint use TLS in email security?
In an Email Firewall Rule, the “Stop Other Rules…” disposition:
What is the primary function of Proofpoint Targeted Attack Protection (TAP)?
|
PDF + Testing Engine
|
|---|
|
$49.5 |
|
Testing Engine
|
|---|
|
$37.5 |
|
PDF (Q&A)
|
|---|
|
$31.5 |
Proofpoint Free Exams |
|---|

|