Under what circumstances will TAP generate an email notification alert?
For which two reasons should organizations customize their incident response plans based on NIST SP 800-61 or another incident response standard? (Select two.)
An analyst is reviewing a quarantined threat within Threat Protection Workbench.

Based on the indicators shown in the exhibit, what is the most likely reason the threat was quarantined?
Heuristic analysis, signature-based detection, and reputation-based methods are all examples of which type of cybersecurity analysis technique?
As a new analyst, you need to review threat intelligence related to threats in your environment. Which Proofpoint product provides this data?
Refer to the exhibit.
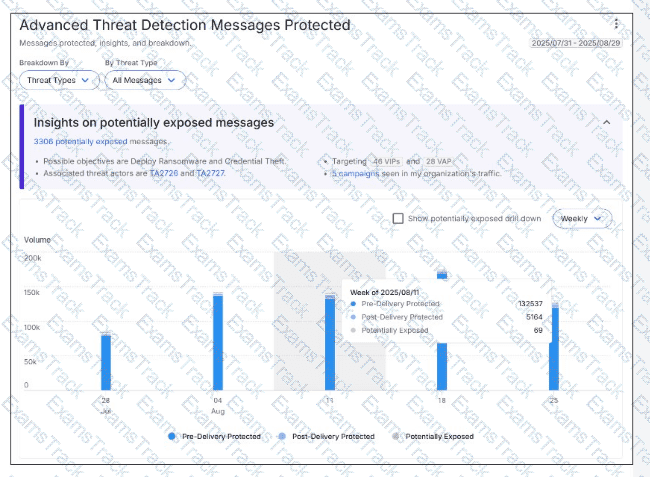
Based on the metrics for the highlighted week, how many malicious messages were blocked by TAP at the email gateway?
Which TAP condemnation results from an analysis of emails submitted via Proofpoint ZenGuide Report Suspicious (formerly PhishAlarm)?
An analyst wants to use the Threats page in TAP Dashboard to review all messages related to a phishing campaign that contain an attachment. What is the correct method to filter these messages?
Which two items should be included in an incident report to be discussed during a post-incident debrief? (Select two.)
In which part of the SMTP conversation can threat actors spoof information to make the message look safe to the recipient?
|
PDF + Testing Engine
|
|---|
|
$49.5 |
|
Testing Engine
|
|---|
|
$37.5 |
|
PDF (Q&A)
|
|---|
|
$31.5 |
Proofpoint Free Exams |
|---|

|