Refer to the exhibit, which shows an ADVPN network.
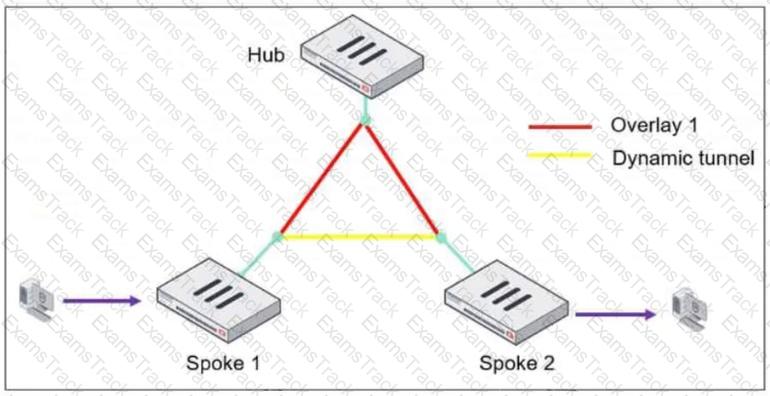
The client behind Spoke-1 generates traffic to the device located behind Spoke-2.
What is the first message that the hub sends to Spoke-1 to bring up the dynamic tunnel?
An administrator is setting up an ADVPN configuration and wants to ensure that peer IDs are not exposed during VPN establishment.
Which protocol can the administrator use to enhance security?
Refer to the exhibit.
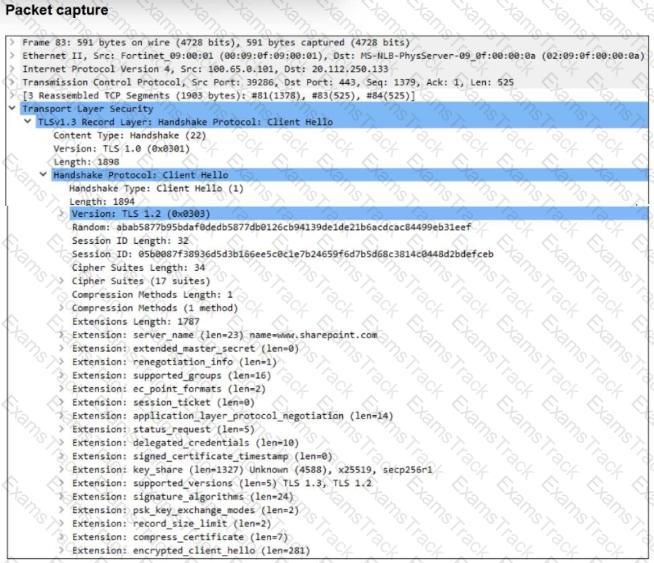
The packet capture output of a client hello message is shown.
You are updating a firewall policy that includes SSL certificate inspection. You are capturing packets from the traffic passing through this firewall policy.
Which two statements about the packet capture are correct? (Choose two.)
Refer to the exhibit, which shows an OSPF network.
Which configuration must the administrator apply to optimize the OSPF database?
During the maintenance window, an administrator must sniff all the traffic going through a specific firewall policy, which is handled by NP6 interfaces. The output of the sniffer trace provides just a few packets.
Why is the output of sniffer trace limited?
You must configure a loopback as a BGP source to connect to the ISP.
Which two commands must you use to establish the connection? (Choose two.)
Refer to the exhibits.
The system administrator settings configured on a root FortiGate and the Security Fabric settings configured on a downstream FortiGate are shown.
When prompted to sign in with Security Fabric to the downstream FortiGate, a user enters the single sign-on (SSO) provider credentials.
What is the result?
You applied a block-all intrusion prevention system (IPS) profile for client and server targets to secure the server but the database team reported that applications stopped working immediately after.
How can you apply IPS in a way that ensures it does not disrupt existing applications in the network?
Refer to the exhibit, which shows a network diagram.
An administrator would like to modify the MED value advertised from FortiGate_1 to a BGP neighbor in the autonomous system 30.
What must the administrator configure on FortiGate_1 to implement this?
An organization ' s guest Internet policy, operating in proxy mode, blocks access to artificial intelligence technology sites using FortiGuard. However, a guest user accessed a page in this category using port 8443.
Which configuration change must you make for FortiGate to analyze HTTPS traffic on nonstandard ports like 8443, when full SSL inspection is active in the guest policy?
|
PDF + Testing Engine
|
|---|
|
$49.5 |
|
Testing Engine
|
|---|
|
$37.5 |
|
PDF (Q&A)
|
|---|
|
$31.5 |
Fortinet Free Exams |
|---|

|