You receive a detection with the following command line:
C:\Windows\system32\cmd.exe /Q /c echo ping -n 1 google.com > \\VICTIM-MACHINE\C$\_______________output 2 > & 1 > C:\Windows\pJYOrvQB.bat & C:\Windows\system32\cmd.exe /Q /c C:\Windows\pJYOrvQB.bat & del C:\Windows\pJYOrvQB.bat
What describes the activity observed?
Which pre-defined reports will show activities that typically indicate suspicious activity occurring on a system?
Your organization uses an internally developed application for operations. The application is triggering Indicators of Attack (IOA) detections for vulnerable driver usage on servers where Falcon was just installed. After reviewing the application, you determine that application behavior is expected. What will reduce risk in the environment the most?
Refer to the image.
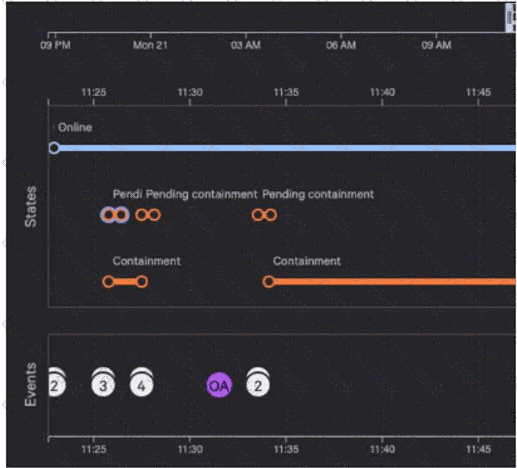
Why are there six pending containment events?
What will the following obfuscated command do?
cmd /c "set x=^n^e^t & set y=@er & set yy=z & set z=r & set r=remove & set f=Domain+ff & set ff=Admin & set g=gumball@ & echo %x%%y:@=us% /%z:r=add% %ff% %g:@=r% | cmd"
A detection contains a suspicious process named "reallysus.exe". This process has a TargetProcessId of 123456789. Which query will return all of the events associated with this process?
Your team received a detection regarding a potentially malicious binary executing on an endpoint. Using CQL (CrowdStrike Query Language), you want to identify all events that relate to this detection. Which field is used to correlate events to this detection?
Refer to the exhibit.
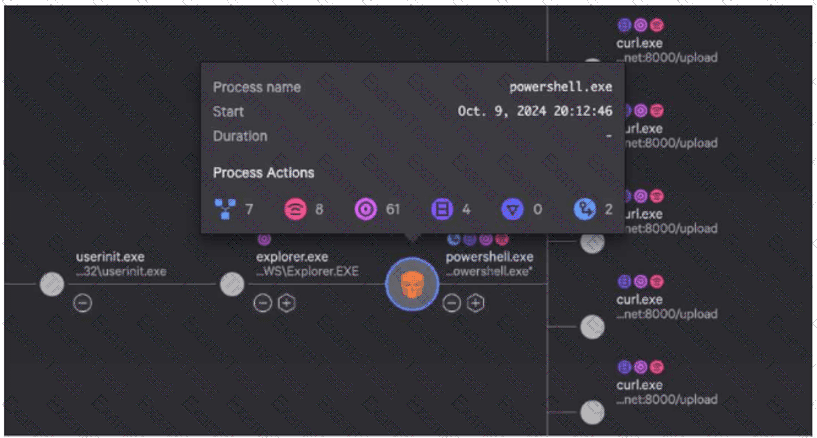
While investigating a process tree, you hover over a malicious powershell.exe process. What is the correct sequence of Process Actions?
|
PDF + Testing Engine
|
|---|
|
$49.5 |
|
Testing Engine
|
|---|
|
$37.5 |
|
PDF (Q&A)
|
|---|
|
$31.5 |
CrowdStrike Free Exams |
|---|

|