You see a large number of command-line processes calling back to an unusual domain that you are reviewing with the Bulk Domain Investigate dashboard. What should your next steps be?
What can a hunter add at the end of a search string in Advanced Event Search to identify outliers when quantifying the results?
Which hunting query's results could indicate that an adversary is performing reconnaissance from a specific host?
You've experienced a ransomware infection that has spread throughout the enterprise. What is the first step you would take to determine the source of infection?
Which built-in hunting report helps you find executables from the Recycle Bin?
An independent investigation team based in Europe asks for the Event Search data to be formatted to Central European Summer Time (CEST). Which parameter within the formatTime() function is required to convert the Unix timestamps?
You receive an alert for the following process tree:
w3wp.exe > powershell.exe > cmd.exe > whoami.exe > net1.exe Which of the following describes what has occurred?
When will the ContextProcessId be the same value as the TargetProcessId?
Refer to the image.
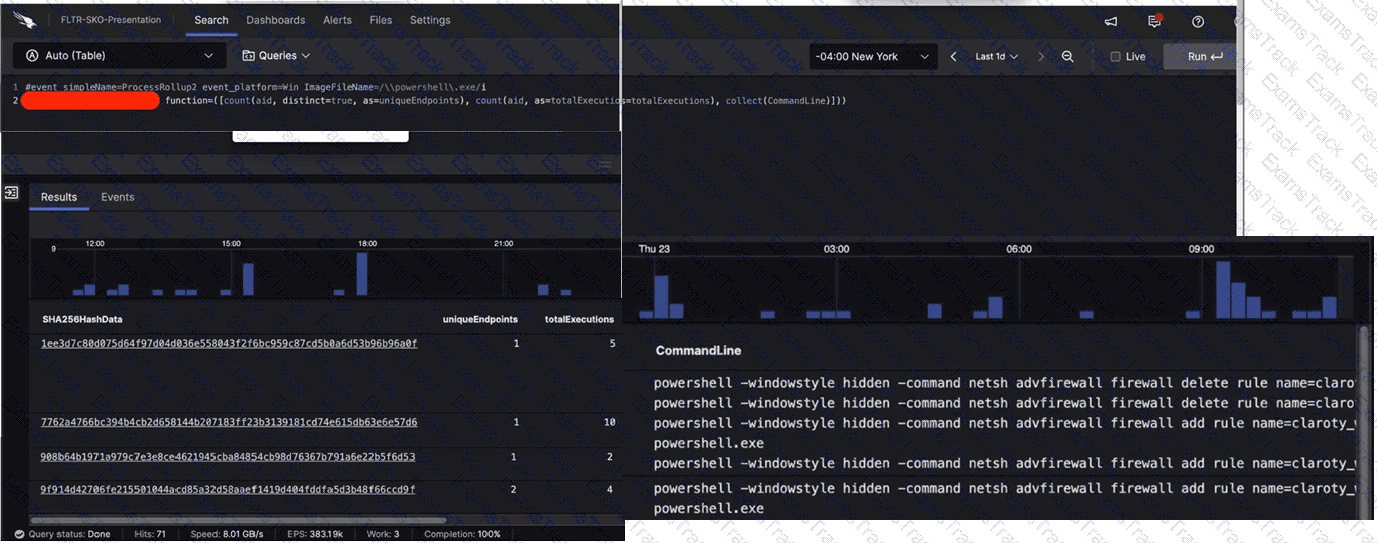
What aggregate function in the CrowdStrike Query Language (CQL) was used to provide the filtered results?
Which Falcon feature creates a graphical view of users, endpoints, and the connections between them by logon type?
|
PDF + Testing Engine
|
|---|
|
$49.5 |
|
Testing Engine
|
|---|
|
$37.5 |
|
PDF (Q&A)
|
|---|
|
$31.5 |
CrowdStrike Free Exams |
|---|

|